Uses Permissions
Go Up to Application Options
Contents
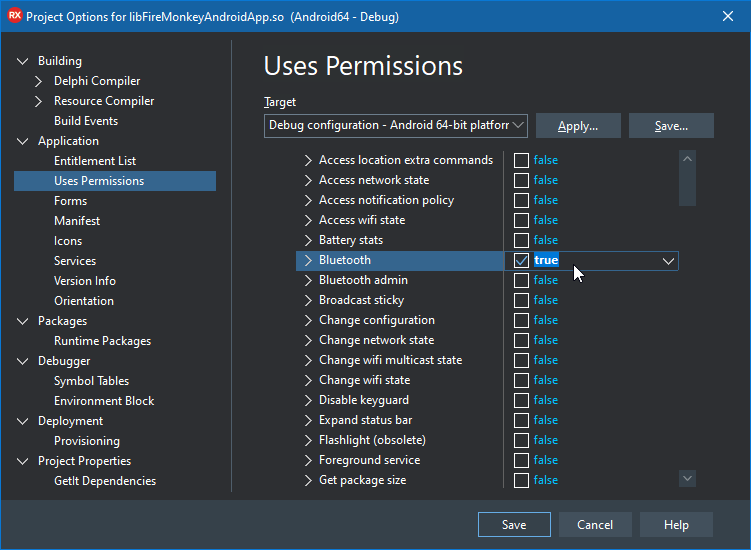
Project > Options > Application > Uses Permissions
Use this dialog box to specify the permissions that your Android application requires to work. RAD Studio adds the permissions you specify in the AndroidManifest.xml file.
Caution: Carefully review the list of permissions that are configured for your Android application. You should disable permissions that your application does not need, because:
- Android devices prompt your users to accept every requested permission when they run your application for the first time.
- Application stores such as Google Play may use permissions to filter out applications.
- For example, if your application requires the Call phone permission (which is required by default), application stores might not let users install your application on tablets.
For example:
- InterBase requires certain permissions:
- Internet: Allows applications to access network sockets. If you are building Client/Server apps accessing remote InterBase databases, this permission is a must-have. This permission is also required by InterBase "call home" silent license registration.
- Read external storage/Write external storage: Allows access to the external storage location where InterBase files, including your database files, are delivered. This permission is required for applications to perform read/write operations.
- Some FireMonkey components require certain permissions. For example:
- TCalendarEdit requires Read calendar and Write calendar permissions.
- TLocationSensor requires Access coarse location and Access fine location permissions.
Some Basic Android Permissions are Set for All FireMonkey Android Apps
New Android applications have the following required permissions set by default:
- Access coarse location
- Access fine location
- Call phone
- Camera
- Internet
- Read external storage
- Read phone state
- Write external storage
INTERNET Permission Is Always Set for the Development Configuration
Your Android apps have several Uses Permissions that are set by default, including the INTERNET permission.
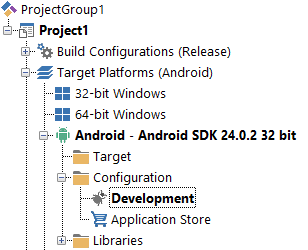
- When you build an Android app with the Configuration set to Development (in the Projects Window), the INTERNET permission is always implicitly set, even if you disable the INTERNET permission on Uses Permissions. This is because the RAD Studio debugger requires the INTERNET permission.
- For the Application Store configuration, however, you can disable the INTERNET permission using Project > Options > Uses Permissions.
Here is the Projects Window with the Development configuration node set for an Android app:
Dialog Box Field Descriptions
| Options | Description |
|---|---|
|
Target, Apply, Save |
See Target Options. |
|
Common items |
Uses Permissions
The following uses permissions can be used as required for most Android applications. Some of the most commonly used basic permissions are preset by RAD Studio when you create an Android app.
Normal Uses Permissions
| Permission Symbol | Permission | Description |
|---|---|---|
|
ACCESS_LOCATION_EXTRA_COMMANDS |
Access location extra commands |
Allows an application to access extra location provider commands. |
|
ACCESS_NETWORK_STATE |
Access network state |
Allows applications to access information about networks. |
|
ACCESS_NOTIFICATION_POLICY |
Access notification policy |
Marker permission for applications that wish to access notification policy. |
|
ACCESS_WIFI_STATE |
Access wifi state |
Allows applications to access information about Wi-Fi networks. |
|
BATTERY_STATS |
Battery stats |
Allows an application to collect battery statistics. |
|
BLUETOOTH |
Bluetooth |
Allows applications to connect to paired Bluetooth devices. |
|
BLUETOOTH_ADMIN |
Bluetooth admin |
Allows applications to discover and pair Bluetooth devices. |
|
BROADCAST_STICKY |
Broadcast sticky |
Allows an application to broadcast sticky intents. These are broadcasts whose data is held by the system after being finished, so that clients can quickly retrieve that data without having to wait for the next broadcast. |
|
CHANGE_CONFIGURATION |
Change configuration |
Allows an application to modify the current configuration, such as locale. |
|
CHANGE_NETWORK_STATE |
Change network state |
Allows applications to change network connectivity state. |
|
CHANGE_WIFI_MULTICAST_STATE |
Change wifi multicast state |
Allows applications to enter Wi-Fi Multicast mode. |
|
CHANGE_WIFI_STATE |
Change wifi state |
Allows applications to change Wi-Fi connectivity state. |
|
DISABLE_KEYGUARD |
Disable keyguard |
Allows applications to disable the keyguard. |
|
EXPAND_STATUS_BAR |
Expand status bar |
Allows an application to expand or collapse the status bar. |
|
FLASHLIGHT |
Flashlight |
Allows access to the flashlight. |
|
FOREGROUND_SERVICE |
Foreground service |
Allows an instant app to create foreground services. |
|
GET_PACKAGE_SIZE |
Get package size |
Allows an application to find out the space used by any package. |
|
GET_TASKS |
Get tasks |
Allows an application to get information about the currently or recently running tasks. |
|
GLOBAL_SEARCH |
Global search |
Allows the global search system to access the data of specific content providers. Typically Global search is used when the provider has some permissions protecting it (which global search would not be expected to hold), and is added as a read-only permission to the path in the provider where global search queries are performed. The Global search permission cannot be held by regular applications; it is used by applications to protect themselves from all other applications except for global search. |
|
INSTALL_SHORTCUT |
Install shortcut |
Allows an application to install a shortcut in Launcher. In Android O (API level 26) and higher, the INSTALL_SHORTCUT broadcast no longer has any effect on your app because it's a private, implicit broadcast. Instead, you should create an app shortcut by using the requestPinShortcut() method from the ShortcutManager class. |
|
INSTANT_APP_FOREGROUND_SERVICE |
Instant app foreground service |
Allows an instant app to create foreground services. |
|
INTERNET |
Internet |
Allows applications to open network sockets. |
|
KILL_BACKGROUND_PROCESSES |
Kill background processes |
Allows an application to call killBackgroundProcesses(String). |
|
MANAGE_OWN_CALLS |
Manage own calls |
Allows a calling application which manages it own calls through the self-managed ConnectionService APIs. |
|
MODIFY_AUDIO_SETTINGS |
Modify audio settings |
Allows an application to modify global audio settings. |
|
NFC |
NFC |
Allows applications to perform I/O operations over NFC. |
|
NFC_TRANSACTION_EVENT |
NFC transaction event |
Allows applications to receive NFC transaction events. |
|
PACKAGE_USAGE_STATS |
Package usage stats |
Allows an application to collect component usage statistics Declaring the permission implies intention to use the API and the user of the device can grant permission through the Settings application. |
|
READ_GSERVICES |
Read GServices |
|
|
READ_SYNC_SETTINGS |
Read sync settings |
Allows applications to read the sync settings. |
|
READ_SYNC_STATS |
Read sync stats |
Allows applications to read the sync stats. |
|
RECEIVE_BOOT_COMPLETED |
Receive boot completed |
Allows an application to receive the ACTION_BOOT_COMPLETED that is broadcast after the system finishes booting. |
|
REORDER_TASKS |
Reorder tasks |
Allows an application to change the Z-order of tasks. |
|
REQUEST_COMPANION_RUN_IN_BACKGROUND |
Request companion run in background |
Allows a companion app to run in the background. |
|
REQUEST_COMPANION_USE_DATA_IN_BACKGROUND |
Request companion use data in background |
Allows a companion app to use data in the background. |
|
REQUEST_DELETE_PACKAGES |
Request delete packages |
Allows an application to request deleting packages. Apps targeting APIs Build.VERSION_CODES.P or greater must hold this permission in order to use Intent.ACTION_UNINSTALL_PACKAGE or PackageInstaller.uninstall(VersionedPackage, IntentSender). |
|
REQUEST_IGNORE_BATTERY_OPTIMIZATIONS |
Request ignore battery optimizations |
Permission an application must hold in order to use Settings.ACTION_REQUEST_IGNORE_BATTERY_OPTIMIZATIONS. This is a normal permission: an app requesting it will always be granted the permission, without the user needing to approve or see it. |
|
SET_ALARM |
Set alarm |
Allows an application to broadcast an Intent to set an alarm for the user. |
|
SET_WALLPAPER |
Set wallpaper |
Allows applications to set the wallpaper. |
|
SET_WALLPAPER_HINTS |
Set wallpaper hints |
Allows applications to set the wallpaper hints. |
|
SUBSCRIBED_FEEDS_READ |
Subscribed feeds read |
Allows an application to allow access the subscribed feeds ContentProvider. |
|
TRANSMIT_IR |
Transmit IR |
Allows using the device's IR transmitter, if available. |
|
USE_BIOMETRIC |
Use biometric |
Allows an app to use device supported biometric modalities. |
|
USE_FINGERPRINT |
Use fingerprint |
Allows an app to use fingerprint hardware. |
|
VENDING_BILLING |
Vending billing (In-app Billing) |
Allows using the In-app Billing service. See the Android documentation for additional information. |
|
VIBRATE |
Vibrate |
Allows access to the vibrator. |
|
WAKE_LOCK |
Wake lock |
Allows using PowerManager WakeLocks to keep processor from sleeping or screen from dimming. |
|
WRITE_SYNC_SETTINGS |
Write sync settings |
Allows applications to write the sync settings. |
|
WRITE_USER_DICTIONARY |
Write user dictionary |
Allows an application to write to the user dictionary. |
The documentation in the Description column of the table above is licensed under Apache 2.0. Copyright © Android Open Source Project.
Dangerous Uses Permissions
The following uses permissions require runtime user approval.
| Permission Symbol | Permission | Description |
|---|---|---|
|
ACCESS_COARSE_LOCATION |
Access coarse location |
Allows an app to access approximate location derived from network location sources such as cell towers and Wi-Fi. |
|
ACCESS_FINE_LOCATION |
Access fine location |
Allows an app to access precise location from location sources such as GPS, cell towers, and Wi-Fi. |
|
ACCESS_MOCK_LOCATION |
Access mock location |
Allows an application to create mock location providers for testing. |
|
ADD_VOICEMAIL |
Add voicemail |
Allows an application to add voicemails into the system. |
|
ANSWER_PHONECALLS |
Answer phonecalls |
Allows the app to answer an incoming phone call. |
|
AUTHENTICATE_ACCOUNTS |
Authenticate accounts |
Allows an application to act as an AccountAuthenticator for the AccountManager. |
|
BODY_SENSORS |
Body sensors |
Allows an application to access data from sensors that the user uses to measure what is happening inside his/her body, such as heart rate. |
|
CALL_PHONE |
Call phone |
Allows an application to initiate a phone call without going through the Dialer user interface for the user to confirm the call being placed. |
|
CAMERA |
Camera |
Required to be able to access the camera device. |
|
CONTINUE_A_CALL_STARTED_IN_ANOTHER_APP |
Continue a call started in another app |
Allows a calling app to continue a call which was started in another app. An example is a video calling app that wants to continue a voice call on the user's mobile network. |
|
GET_ACCOUNTS |
Get accounts |
Allows access to the list of accounts in the Accounts Service. |
|
MANAGE_ACCOUNTS |
Manage accounts |
Allows an application to manage the list of accounts in the AccountManager. |
|
PROCESS_OUTGOING_CALLS |
Process outgoing calls |
Allows an application to monitor, modify, or abort outgoing calls. |
|
READ_CALENDAR |
Read calendar |
Allows an application to read the user calendar data. |
|
READ_CALL_LOG |
Read call log |
Allows an application to read the user call log. |
|
READ_CONTACTS |
Read contacts |
Allows an application to read the user contacts data. |
|
READ_EXTERNAL_STORAGE |
Read external storage |
Allows an application to read from external storage. |
|
READ_HISTORY_BOOKMARKS |
Read history bookmarks |
Allows an application to read (but not write) the user browsing history and bookmarks. |
|
READ_PHONE_NUMBERS |
Read phone numbers |
Allows read access to the device's phone number(s). This is a subset of the capabilities granted by READ_PHONE_STATE but is exposed to instant applications. |
|
READ_PHONE_STATE |
Read phone state |
Allows read only access to phone state. |
|
READ_PROFILE |
Read profile |
Allows an application to read the user personal profile data. |
|
READ_SMS |
Read SMS |
Allows an application to read SMS messages. |
|
READ_SOCIAL_STREAM |
Read social stream |
Allows an application to read from the user social stream. |
|
READ_USER_DIRECTORY |
Read user dictionary |
Allows an application to read the user dictionary. |
|
RECEIVE_BOOT_COMPLETED |
Receive boot completed |
Allows an application to receive the ACTION_BOOT_COMPLETED that is broadcast after the system finishes booting. |
|
RECEIVE_SMS |
Receive mms |
Allows an application to monitor incoming MMS messages, to record or perform processing on them. |
|
RECEIVE_WAP_PUSH |
Receive WAP push |
Allows an application to monitor incoming WAP push messages. |
|
RECORD_AUDIO |
Record audio |
Allows an application to record audio. |
|
SEND_SMS |
Send SMS |
Allows an application to send SMS messages. |
|
SUBSCRIBED_FEEDS_WRITE |
Subscribed feeds write |
Allows an application to allow write the subscribed feeds ContentProvider. |
|
UNINSTALL_SHORTCUT |
Uninstall shortcut |
Don't use this permission in your app. This permission is no longer supported. |
|
USE_CREDENTIALS |
Use credentials |
Allows an application to request authtokens from the AccountManager. |
|
USE_SIP |
Use SIP |
Allows an application to use SIP service. |
|
WRITE_CALENDAR |
Write calendar |
Allows an application to write (but not read) the user calendar data. |
|
WRITE_CALL_LOG |
Write call log |
Allows an application to write (but not read) the user contacts data. |
|
WRITE_CONTACTS |
Write contacts |
Allows an application to write (but not read) the user contacts data. |
|
WRITE_EXTERNAL_STORAGE |
Write external storage |
Allows an application to write to external storage. |
|
WRITE_HISTORY_BOOKMARKS |
Write history bookmarks |
Allows an application to write (but not read) the user browsing history and bookmarks. |
|
WRITE_PROFILE |
Write profile |
Allows an application to write (but not read) the user personal profile data. |
|
WRITE_SMS |
Write SMS |
Allows an application to write SMS messages. |
|
WRITE_SOCIAL_STREAM |
Write social stream |
Allows an application to write (but not read) the user social stream data. |
The documentation in the Description column of the table above is licensed under Apache 2.0. Copyright © Android Open Source Project.
Signature Uses Permissions
The following uses permissions require a matching certificate.
| Permission Symbol | Permission | Description |
|---|---|---|
|
BIND_ACCESSIBILITY_SERVICE |
Bind accessibility service |
Must be required by an AccessibilityService, to ensure that only the system can bind to it. |
|
BIND_AUTOFILL_SERVICE |
Bind autofill service |
Must be required by a AutofillService, to ensure that only the system can bind to it. |
|
BIND_CALL_SCREENING_SERVICE |
Bind call screening service |
Must be required by a CallScreeningService, to ensure that only the system can bind to it. |
|
BIND_CARRIER_MESSAGING_SERVICE |
Bind carrier messaging service |
This constant was deprecated in API level 23. Use BIND_CARRIER_SERVICES instead. |
|
BIND_CARRIER_SERVICES |
Bind carrier services |
The system process that is allowed to bind to services in carrier apps will have this permission. Carrier apps should use this permission to protect their services that only the system is allowed to bind to. |
|
BIND_CHOOSER_TARGET_SERVICE |
Bind chooser target service |
Must be required by a ChooserTargetService, to ensure that only the system can bind to it. |
|
BIND_CONDITION_PROVIDER_SERVICE |
Bind condition provider service |
Must be required by a ConditionProviderService, to ensure that only the system can bind to it. |
|
BIND_DEVICE_ADMIN |
Bind device admin |
Must be required by device administration receiver, to ensure that only the system can interact with it. |
|
BIND_DREAM_SERVICE |
Bind dream service |
Must be required by an DreamService, to ensure that only the system can bind to it. |
|
BIND_INCALL_SERVICE |
Bind in-call service |
Must be required by a InCallService, to ensure that only the system can bind to it. |
|
BIND_INPUT_METHOD |
Bind input method |
Must be required by an InputMethodService, to ensure that only the system can bind to it. |
|
BIND_MIDI_DEVICE_SERVICE |
Bind MIDI device service |
Must be required by an MidiDeviceService, to ensure that only the system can bind to it. |
|
BIND_NFC_SERVICE |
Bind NFC service |
Must be required by a HostApduService or OffHostApduService to ensure that only the system can bind to it. |
|
BIND_NOTIFICATION_LISTENER_SERVICE |
Bind notification listener service |
Must be required by an NotificationListenerService, to ensure that only the system can bind to it. |
|
BIND_PRINT_SERVICE |
Bind print service |
Must be required by a PrintService, to ensure that only the system can bind to it. |
|
BIND_QUICK_SETTINGS_TILE |
Bind Quick Settings tile |
Allows an application to bind to third party quick settings tiles.
Should only be requested by the System, should be required by TileService declarations. |
|
BIND_REMOTEVIEWS |
Bind remoteviews |
Must be required by a RemoteViewsService, to ensure that only the system can bind to it. |
|
BIND_TELECOM_CONNECTION_SERVICE |
Bind telecom connection service |
Must be required by a ConnectionService, to ensure that only the system can bind to it. |
|
BIND_TEXT_SERVICE |
Bind text service |
Must be required by a TextService. |
|
BIND_TV_INPUT |
Bind TV input |
Must be required by a TvInputService to ensure that only the system can bind to it. |
|
BIND_VISUAL_VOICEMAIL_SERVICE |
Bind visual voicemail service |
Must be required by a link VisualVoicemailService to ensure that only the system can bind to it. |
|
BIND_VOICE_INTERACTION |
Bind voice interaction |
Must be required by a VoiceInteractionService, to ensure that only the system can bind to it. |
|
BIND_VPN_SERVICE |
Bind VPN service |
Must be required by an VpnService, to ensure that only the system can bind to it. |
|
BIND_VR_LISTENER_SERVICE |
Bind VR listener service |
Must be required by an VrListenerService, to ensure that only the system can bind to it. |
|
BIND_WALLPAPER |
Bind wallpaper |
Must be required by a WallpaperService, to ensure that only the system can bind to it. |
|
CLEAR_APP_CACHE |
Clear app cache |
Allows an application to clear the caches of all installed applications on the device. |
|
MANAGE_DOCUMENTS |
Manage documents |
Allows an application to manage access to documents, usually as part of a document picker.
This permission should only be requested by the platform document management app. This permission cannot be granted to third-party apps. |
|
READ_VOICEMAIL |
Read voicemail |
Allows an application to read voicemails in the system. |
|
REQUEST_INSTALL_PACKAGES |
Request install packages |
Allows an application to request installing packages. Apps targeting APIs greater than 25 must hold this permission in order to use Intent.ACTION_INSTALL_PACKAGE. |
|
SYSTEM_ALERT_WINDOW |
System alert window |
Allows an application to open windows using the type TYPE_SYSTEM_ALERT, shown on top of all other applications. |
|
WRITE_SETTINGS |
Write settings |
Allows an application to read or write the system settings. |
|
WRITE_VOICEMAIL |
Write voicemail |
Allows an application to modify and remove existing voicemails in the system. |
The documentation in the Description column of the table above is licensed under Apache 2.0. Copyright © Android Open Source Project.