Enabling LDAP Authentication
Go Up to Overview of User Accounts
To enable the Lightweight Directory Access Protocol (LDAP) so that LDAP users can log in to ER/Studio Team Server, do the following:
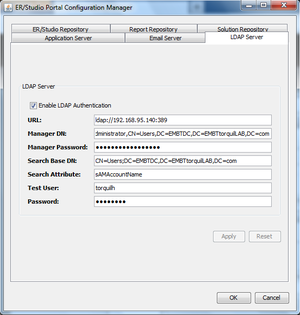
- Open the ER/Studio Team Server Configuration Manager.
- On the LDAP Server tab, check Enable LDAP Authentication.
- In the URL field, enter the URL of the server running LDAP. For example, ldap://10.40.40.94:389 for normal connections, or ldaps://10.40.40.94:636 for secure connections.
- In the Manager DN field, enter the distinguished name for the user that is used to authenticate users. ER/Studio Team Server uses this account to connect to the LDAP server and validate user credentials. For example, CN=administrator,CN=Users,DC=mydomain,DC=com.
- Note: In this example, administrator has been used, it does not need to be administrator but an account able to authenticate via LDAP. In which case the Users is defined as a container rather than an organizational unit as is the Microsoft Active Directory default. Your user accounts may be in an organizational unit, in this case you would specify it differently, for example, CN=user name,OU=sales,DC=mydomain,DC=com
To find the correct DN for your user in Microsoft Active Directory you can use the dsquery command from a command prompt on the AD server. For example:dsquery user -name admin*
- In the Manager Password field, enter the password for the validating user account.
- In the Search Base DN field, enter the name of the root node in LDAP from which to search for users. For example, CN=Users;DC=mydomain,DC=com.
- In the Search Attribute field, enter the attribute in LDAP holding the user's login name. For example, sAMAccountName (for ActiveDirectory).
- In the Test User field, enter the username of a sample user account to attempt to authenticate against the LDAP server. The Apply button uses this information to validate the specified LDAP information before continuing.
- In the Password field, enter the password of the specified Test User account.
- Click Apply.
LDAP authentication is now enabled.